Operating Systems for Hacking are the most important value in technology. Many individuals regard “hacking” as a sinister and unlawful activity. However, this is not the case. Hacking has always been an aspect of computing, and it covers a considerably broader range of topics than you might assume. An ethical hacker’s job is to find flaws or weak spots in a network, hacker operating system, or any other protocol.
There are many people that want to study ethical hacking. There are Operating Systems for Hacking courses accessible on the internet best linux for hacking that may help you grasp ethical hacking in a matter of years. If you want to learn to linux hacking os hack, you should start using the Linux distribution right now.
List of 12 Operating Systems For Ethical Hacking
This post has chosen to give a list of the top Linux-based operating systems used by hackers. So, let’s take a look at the top hacking operating systems.
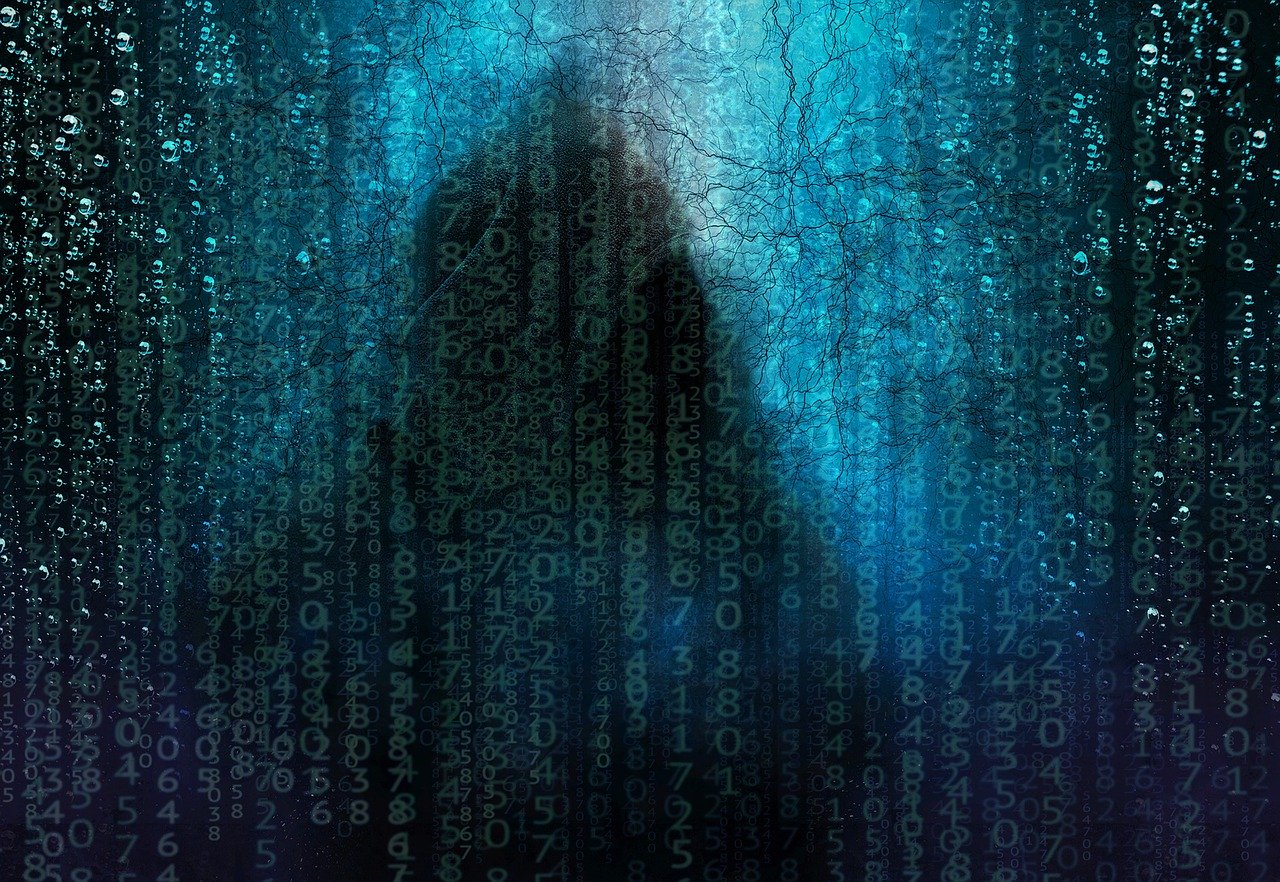
1. Nodezero
Nodezero, an operating system based on Ubuntu, is frequently used by ethical hackers. Because it uses the same Ubuntu hacking os Repository as Ubuntu, Nodezero receives updates whenever Ubuntu hacking operating system does. Furthermore, Nodezero offers over 300 distinct tools to aid you with penetration testing and security best linux for hacking research. On NodeZero, you will find tools for every other security purpose.
2. BackTrack
Backtrack is another excellent and frequently used Linux-based operating system for penetration testing and security research. However, You won’t believe it, but the operating system gives users hacking operating system access to a variety of security-related features, including port scanning, security auditing, WiFi inspection, and hacker operating system more. Because Backtrack is a portable best linux for hacking tool that does not require installation, it can be run immediately from the USB. Also Check: What is Lucky Patcher, and is it legal?
3. Pentoo
4. Kali Linux
By far the most popular Linux distribution for digital forensics and penetration testing is Kali Linux. You won’t believe it when I tell you that the operating system has over 600 penetration-testing applications. Secondly, It accepts 32-bit and 64-bit images for hacker operating system usage with x86 machines. Moreover, Kali Linux also supports a linux hacking os variety best linux for hacking of development boards, including the BeagleBone, Odroid, CuBox, Raspberry Pi, and others.
5. Bugtraq
Bugtraq is a GNU/Linux distribution targeted at digital hacking os forensics, penetration testing, Malware Laboratories, and GSM Forensics, and is one of the finest hacking operating system choices for attackers. However, The operating system includes a variety of tools such as forensic tools, malware testing tools, audit tools, network tools, and so on.
6. Parrot Security OS
It is an operating system that combines Debian GNU/Linux with Frozen Box OS and Kali Linux to provide attackers and security testers with the greatest penetration and security testing experience possible. Moreover, The Frozen Box Dev Team created it as an Operating Systems For Ethical Hacking operating system linux hacking os for IT security and penetration testing.
7. ArchStrike
This is one of the most effective Linux distributions for hacking. It is a penetration testing and security layer built on top of the well-known Arch Strike Linux hacking operating system distribution. The operating system hacker operating system adheres to Arch Linux’s principles, and it is an Arch Linux repository for security professionals, complete with a plethora of tools.
8. Dracos Linux
Dracos Linux is the final operating system on the list, and it is a favourite among hackers. However, The operating system, which is built on Linux from the ground up, is frequently used by hackers. What do you think? Dracos Linux is quick, dependable, and feature-rich. Moreover, When it comes linux hacking os to functionality, the operating system includes a plethora of security testing tools.
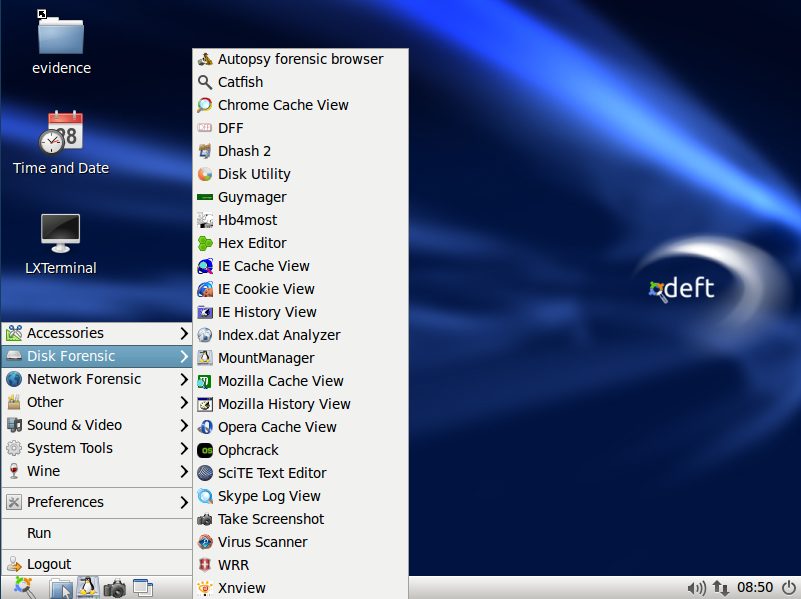
9. DEFT Linux
The Digital Evidence and Forensic Toolkit (DEFT) is a Linux distribution based on the Digital Advanced Response Toolkit (DART) software. In addition, Deft is an Ubuntu customising tool. However, DEFT Linux includes best linux for hacking computer forensics and incident response Operating Systems For Ethical Hacking tools that can be used by IT auditors, investigations, military, and police.
10. Caine
Caine is a live disk-base security-focus distro base on Ubuntu. However, It is an abbreviation for Computer Aided Investigation Environment, and it can be launch directly from the hard disc after installation. In addition, This Linux distribution includes a plethora of tools to aid you in system forensics. Lastly, Caine has a linux hacking os plethora of database, memory, forensics, and network analysis applications.
11. DemonLinux
DemonLinux is a hacking-oriented Linux distribution. In addition, It has a minimal hacking operating system desktop environment. This platform has a dark look linux hacking os and an easy-to-use user interface. Finally, DemonLinux allows you to search for or access anything with a single keystroke.
12. Samurai web testing framework
The Samurai Web Testing Framework is a virtual machine for web penetration testing that is based on open source software. Secondly, This framework is a virtual computer linux hacking os that is compatible with VirtualBox and VMware and is pre-configure to act as an online pen-testing environment. Moreover, The VM includes the top open source and free Operating Systems For Ethical Hacking tools for testing and attacking websites.
Final Words
Choosing the best operating system for hacking and penetration testing is a positive sign that you are ready to master ethical hacking and penetration testing principles in order to improve your abilities and protect enterprise assets from cybercriminals. Furthermore, Every security professional has a favourite security operating system for using hacking tools for both learning and commercial purposes. Finally, You can try all of the operating systems at least once to get a feel for the outstanding features.